Cloud-Native Security Model Explained
It’s common for companies to be using old security policies that haven’t adapted to the times. However, Cloud-native elements make it difficult for these policies to keep up with the complexity and scale of these new developments. As a result, organizations often put security lower down on their priority list. DevSecOps caused companies to pay more attention to their security flaws.
However, this alone isn’t enough to prevent cyberattacks in cloud-native environments. In today’s world, companies need to put security on the same priority level as the development because attackers have been taking advantage of cloud-native environments to access a company’s system.
Furthermore, many organizations create their systems using public clouds and open-source environments which they don’t own. Also, they use code by taking it from open-source environments. Adding these third-party elements into the mix can lead to more security vulnerabilities if left unchecked.
Therefore, understanding how to create a solid cloud-native security model can help your company prevent and minimize potential threats. This article covers the main areas to consider when securing cloud-native models.
Source Code

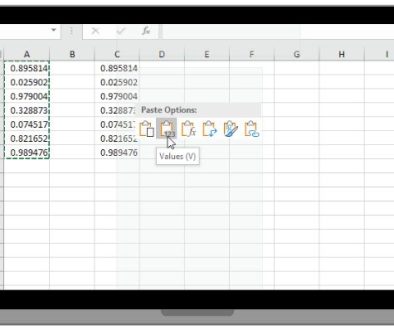
Vulnerabilities in your source code can cause major issues down the line. Static Code Analysis is one of the effective ways to reduce security risks in code. Also, various tools are available that automatically analyze the code in a dormant state.
The tool then provides you with an analysis of what it discovered which you can use to find weak areas that you need to strengthen. Without these tools, it can be difficult trying to scan for flaws in your code manually.
It’s also common practice for companies to use both dynamic application and static application security testing. Such testing ensures that you can prevent cybercriminals from carrying out attacks in your applications through cross-site scripting and SQL injection.
Companies should also be cautious not to reveal ports or tunnels unnecessarily to prevent giving hackers the chance to exploit vulnerabilities.
Strengthening Containers
After developers have created an app within a container, they need to keep a few key things in mind regarding the storage and deployment of the app.
Since you don’t need root access to use most applications, it’s best not to use privileged containers. Only actions such as monitoring require root access to use. Putting this into practice prevents attackers from having the opportunity to gain access to host nodes and taking control.
Moreover, boosting the security of your container isolation features is also recommended. In addition to this, you should perform container and image scanning. Be sure to scan container images when they’re resting and see if the tool you’re using provides reports on any vulnerabilities.
Lastly, image signing is a process to think about implementing too. Image signing works by integrating infrastructure from public keys and providing details on whether or not the images have experienced any interference throughout the development stages.
How to Secure Clusters

Ensuring that your clusters are secured is incredibly important to keeping your containers free from vulnerabilities. It also makes it easier to scale your containers at a later stage. So, be sure to implement different certificates or renew them regularly so that they’re up to date. It would be best to ensure that the data is appropriately encrypted while it’s resting to prevent hackers from gaining access.
Many organizations reduce the number of administrators that can access the clusters. The fewer administrative users you have, the easier it is to limit cyber attacks. Moreover, disabling access to the public is highly recommended to prevent exploiting vulnerabilities.
When it comes to the applications that are functioning within the cluster, you can do several things to boost security which include the following:
- Make sure that external access is appropriately secured
- Reduce the amount of traffic happening among applications within clusters that are utilizing network policies
- Take control of access to API servers and put authentication and authorization processes in place
- Integrating pod security policies is an excellent method to prevent privileged containers
- Organizations need to check the documents of their cluster or cloud supplier, which helps developers properly secure cluster environments and applications
API Security

Security issues with API are a significant weak point for many cloud-native apps. It’s recommended to use HTTPS for all your company’s communications to minimize vulnerabilities. Organizations also include cryptographic hashes that enable data to remain confidential at all times, regardless of whether it was stolen.
Furthermore, you should never share information such as API keys and passwords across URLs. In addition, using stateless APIs keeps your network more secure as you have to go through authentication processes in real-time, which eliminates the risk from previous sessions and cookies.
It’s also best not to use cached permissions when validating credentials, as this provides cybercriminals with an access point to user sessions.
Boosting Cloud Security

Containers function in the cloud, ensuring that your cloud security is boosted imperative to keeping your containers safe. Misconfigurations or security flaws that are left unchecked provide hackers with access points that can enable them to see and steal data and code.
The most used cloud providers include security guidelines that companies should adhere to. These guidelines provide you with details about tools and documents that developers can use to ensure your organization’s cloud system is secured.
Therefore, cloud networks with fewer misconfigurations and threats discovered early will provide you with a higher level of security.
Shared Responsibility Models
A shared responsibility model is included with cloud service suppliers. The provider deals with maintaining elements such as the network and infrastructure while developers are responsible for keeping operating systems, user access, data, and applications secured.
Moreover, the cloud supplier has control over certain elements which are out of your control. As a result, it’s best to use tools that the cloud supplier provides so that you can monitor for any security threats. You can then notify them if you notice any security threats that require their attention.
Conclusion
Keeping your cloud network secured using the native security model outlined above effectively prevents attackers from exploiting your system. It focuses on ensuring that developers reduce misconfigurations and make security a priority.
Large organizations understand the need to ditch old security policies and tools and integrate up-to-date technologies and systems to secure their cloud networks. Hopefully, the information found throughout this text has provided you with some insight into how you can go about boosting your cloud security.
- Pros and Cons of Virtual Private Networks in 2023 - March 4, 2023
- How Do I Keep My Logo From Being Stolen - February 27, 2023
- Create a User-Friendly Admin Panel for Any Database - October 13, 2022
Where Should We Send
Your WordPress Deals & Discounts?
Subscribe to Our Newsletter and Get Your First Deal Delivered Instant to Your Email Inbox.